Socialist millionaires
In cryptography, the socialist millionaire problem[1] is one in which two millionaires want to determine if their wealth is equal without disclosing any information about their riches to each other. It is a variant of the Millionaire's Problem[2][3] whereby two millionaires wish to compare their riches to determine who has the most wealth without disclosing any information about their riches to each other.
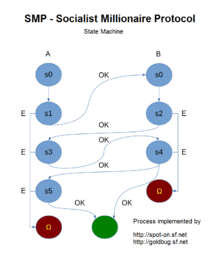
It is often used as a cryptographic protocol that allows two parties to verify the identity of the remote party through the use of a shared secret, avoiding a man-in-the-middle attack without the inconvenience of manually comparing public key fingerprints through an outside channel. In effect, a relatively weak password/passphrase in natural language can be used.
Motivation
Alice and Bob have secret values and , respectively. Alice and Bob wish to learn if without allowing either party to learn anything else about the other's secret value.
A passive attacker simply spying on the messages Alice and Bob exchange learns nothing about and , not even whether .
Even if one of the parties is dishonest and deviates from the protocol, that person cannot learn anything more than if .
An active attacker capable of arbitrarily interfering with Alice and Bob's communication (a man-in-the-middle) cannot learn more than a passive attacker and cannot affect the outcome of the protocol other than to make it fail.
Therefore, the protocol can be used to authenticate whether two parties have the same secret information. Popular instant message cryptography package Off-the-Record Messaging uses the Socialist Millionaire protocol for authentication, in which the secrets and contain information about both parties' long-term authentication public keys as well as information entered by the users themselves.
Off-the-Record Messaging protocol
A prime, , and any non-identity element, , of are agreed on before the protocol, and in practice are generally fixed in a given implementation. For example, in the Off-the-Record Messaging protocol, is a specific fixed 1,536-bit prime. is then a generator of , and all operations are performed modulo , or in other words, in the multiplicative group, .
By , denote the secure multiparty computation, Diffie–Hellman–Merkle key exchange, which, for the integers, , returns to each party:
- Alice calculates and sends it to Bob, who then calculates .
- Bob calculates and sends it to Alice, who then calculates .
as is Abelian. Note that this procedure is insecure against man-in-the-middle attacks.
The Socialist millionaire protocol only has a few steps that are not part of the above procedure, and the security of each relies on the difficulty of the discrete logarithm problem, just as the above does. All sent values also include zero-knowledge proofs that they were generated according to protocol.
Part of the security also relies on random secrets. However, as written below, the protocol is vulnerable to poisoning if Alice or Bob chooses any of , , , or to be zero. To solve this problem, each party must check during the Diffie-Hellman exchanges that none of the or that they receive is equal to 1. It is also necessary to check that and .
| Alice | Multiparty | Bob | |
|---|---|---|---|
| 1 | Message Random |
Public | Message Random |
| 2 | Secure | ||
| 3 | Secure | ||
| 4 | Test , | Test , | |
| 5 | |||
| 6 | Insecure exchange | ||
| 7 | Secure | ||
| 8 | Test , | Test , | |
| 9 | Test | Test |
Note that:
and therefore
- .
Because of the random values stored in secret by the other party, neither party can force and to be equal unless equals , in which case . This proves correctness.
See also
References
- ↑ Andrew Yao (1982). "Protocols for secure communications" (PDF). Proc. 23rd IEEE Symposium on Foundations of Computer Science (FOCS '82). pp. 160–164. doi:10.1109/SFCS.1982.88.
- ↑ Andrew Yao (1986). "How to generate and exchange secrets" (PDF). Proc. 27th IEEE Symposium on Foundations of Computer Science (FOCS '86). pp. 162–167. doi:10.1109/SFCS.1986.25.
External links
- Description of the OTR-Messaging Protocol version 2
- The Socialist Millionaire Problem - Explain it like I'm Five
- Goldbug Messenger, which uses an implementation the Socialist Millionaire Protocol